Cisco
200-201
Q1:
Which of these is a defense-in-depth strategy principle?
○
A
identify the minimum resource required per employee.○
B
Assign the least network privileges to segment network permissions.○
C
Provide the minimum permissions needed to perform Job functions.○
D
Disable administrative accounts to avoid unauthorized changes.
Cisco
200-201
Q2:
Which type of attack uses a botnet to reflect requests off of an NTP server to overwhelm a target?
○
A
Display○
B
Man-in-the-middle○
C
Distributed denial of service○
D
Denial of service
Cisco
200-201
Q3:
What is data encapsulation?
○
A
Browsing history is erased automatically with every session.○
B
The protocol of the sending host adds additional data to the packet header.○
C
Data is encrypted backwards, which makes it unusable.○
D
Multiple hosts can be supported with only a few public IP addresses.
Cisco
200-201
Q4:
A security engineer must investigate a recent breach within the organization. An engineer noticed that a breached workstation is trying to connect to the domain "Ranso4730-mware92-647". which is known as malicious. In which step of the Cyber Kill Chain is this event?
○
A
Vaporization○
B
Delivery○
C
reconnaissance○
D
Action on objectives
Cisco
200-201
Q5:
Refer to the exhibit.
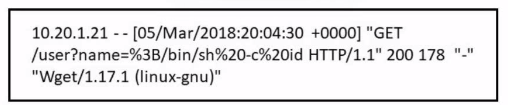
Which attack is being attempted against a web application?
○
A
SQL injection○
B
man-in-the-middle○
C
command injection○
D
denial of service